Faculty
Post-Docs
PhD Students
PhD Alums
- Hristo Bojinov
- Andrew Bortz
- Benedikt Bünz
→ Prof. at NYU - Henry Corrigan-Gibbs
→ Prof. at U.C.B - Glenn Durfee
- Saba Eskandarian
→ Prof. at UNC - Ben Fisch
→ Prof. at Yale - Craig Gentry
→ CTO TripleBlind - Eu-Jin Goh
- Philippe Golle
- Mike Hamburg
- Jeremy Horwitz
- Sam Kim
- Dima Kogan
→ CTO Fordefi - Kevin Lewi
- Ben Lynn
- Mike Malkin
- Yan Michalevsky
- Ilia Mironov
- Nagendra Modadugu
- Hart Montgomery
- Wilson Nguyen
- Valeria Nikolaenko
- Alex Ozdemir
→ Prof. at G.Tech - Neil Perry
- Ananth Raghunathan
- Hovav Shacham
→ Prof. at UCSD - Nusret Tas
- Florian Tramèr
→ Prof. at ETH - Riad S. Wahby
→ Prof. at CMU - David Wu
→ Prof. at U.T.Austin - Mark Zhandry
→ Prof. at Stanford - Joe Zimmerman
Post-Doc Alums
- Joseph Bonneau
→ Prof. at NYU - Zvika Brakerski
→ Prof. at Weizmann - David Freeman
- Suman Jana
→ Prof. at Columbia - Stanislaw Jarecki
→ Prof. at U.C.I - Arvind Narayanan
→ Prof. at Princeton - Lior Rotem
→ Prof. at HUJI - Gil Segev
→ Prof. at HUJI - Brent Waters
→ Prof. at U.T.Austin
Web Page Alums
The Applied Crypto Group is a part of the Security Lab in the Computer Science Department at Stanford University. Research projects in the group focus on various aspects of network and computer security. In particular the group focuses on applications of cryptography to real-world security problems. For more information follow the links below.
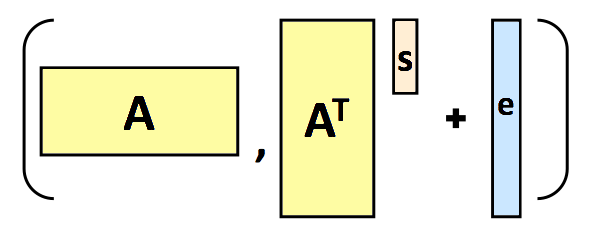
Lattices in Cryptography
Integer lattices have found many applications in cryptography: in proofs of security, in attacks, and in constructing cryptosystems.
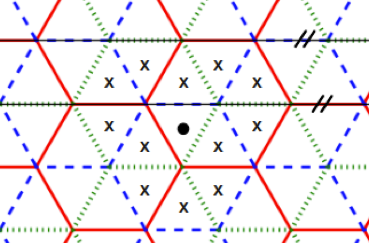
Privacy
Can multi-user services operate without sending all user data to the cloud in the clear? Some examples include private location-based services, private computation of aggregate statistics, private recommendation systems, private queries to a database, and anonymous messaging.
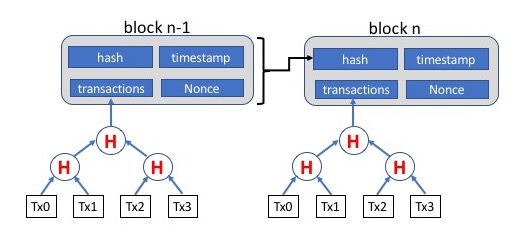
Blockchain technologies
We are developing cryptographic tools with applications to blockchains. We are also teaching a course on the topic, CS251.
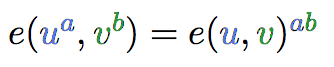
Pairings-Based Cryptography
Cryptographic pairings have numerous applications to cryptography, including everything from identity-based encryption and short digital signatures to broadcast encryption and search-friendly encryption.
Computer and Web Security
Computer security research explores architectures that improve software security and enhances our understanding of attack strategies. Our research covers SSL and TLS, Web security, and areas of operating systems security.
Projects
Bulletproofs: Short Proofs for Confidential Transactions and More
Prio: Private, Robust, and Scalable Computation of Aggregate Statistics
Balloon Hashing: Memory-Hard Password Hashing
PowerSpy: Location Tracking using Mobile Device Power Analysis
Riposte: An Anonymous Messaging System Handling Millions of Users
Gyrophone: Recognizing Speech from Gyroscope Signals
PORTIA: Managing sensitive information in a wired world
Location privacy
Identity Based Encryption email system (IBE secure email)
The ITTC project: Intrusion tolerance via threshold cryptography
Export Control Warning: The US Government regulates the physical export or transmission of cryptographic source and corresponding object code outside the borders of the US and within the US when the recipient is an embassy or an affiliate of a foreign government. Posting encrypted code to the internet and making it publicly available is considered an export and may entail US government notification requirements. Please see Stanford's Export Control Encryption Page if you have a need to take, transfer or transmit Stanford-generated encryption code outside of the US or to share it with US-based representatives of foreign governments.